Blog
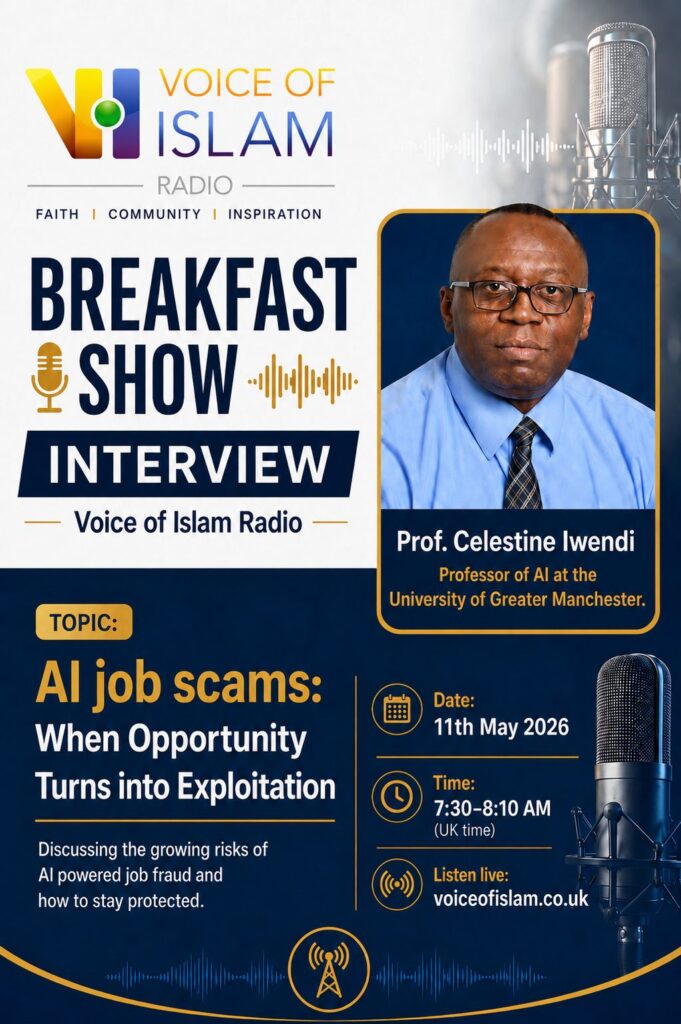
Identifying AI-Powered Job Scams: Insights from Prof. Celestine Iwendi on Voice of Islam Radio
In a recent interview on the Voice of Islam Radio Breakfast Show, Prof. Celestine Iwendi, a leading expert at the CIOTH Lab, delved into the dark side of Artificial Intelligence: the rise of highly sophisticated, AI-driven job scams.
As AI continues to revolutionize industries, it is also being used to create “polished but fake” job opportunities that target vulnerable students and recent graduates. Below are summarized key takeaways from the interview to help you stay safe.
1. The Anatomy of an AI Scam
Prof. Iwendi highlights that these scams often use AI to generate professional-sounding job descriptions and personalized messages. However, they usually share common red flags:
-
Unrealistic Compensation: Offers that seem too good to be true (e.g., £1,000 for a few hours of simple work).
-
High-Pressure Tactics: Demands to respond within 24–48 hours or move the conversation to unencrypted platforms like WhatsApp.
-
Vague Responsibilities: A lack of specific reporting lines or clearly defined tasks.
2. Guarding Your Digital Identity
One of the most critical points discussed was data privacy. Prof. Iwendi warned that scammers often use “onboarding” as a ruse to steal sensitive information:
-
Never share: Bank details, National Insurance numbers, or passport scans before receiving a formal, verified contract.
-
Beware of “Pay-to-Work”: Legitimate companies will never ask an applicant to pay for software licenses, background checks, or training.
3. The CIOTH Lab Mission: Proactive Defense
At the CIOTH Lab, we believe in predictive security. Rather than waiting for a breach to happen, we are developing algorithms including our own “Anti-Cheat” protocols to detect fraudulent patterns before they reach the user.
“AI will take the jobs of those who don’t know AI,” Prof. Iwendi noted, emphasizing that digital literacy is our best defense. By understanding how these models work, we can better identify when they are being used maliciously.
Stay Connected: For more insights into the intersection of AI, IoT, and Security, follow our updates here at the CIOTH Lab.